Adder Technology’s latest IP KVM system, the AdderLink Infinity 3000 is the first in its range to allow control over virtual machines.
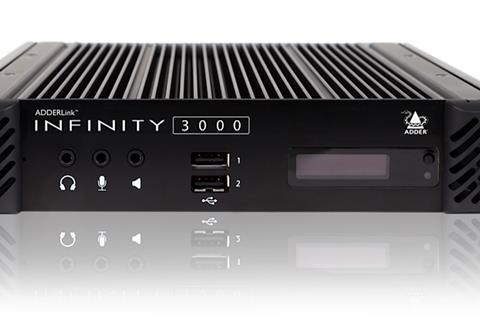
Adder Technology’s latest IP KVM system, the AdderLink Infinity 3000 is the first in its range to allow control over virtual machines, for instant switching between unlimited virtual and physical environments from a single human machine interface.
Built on Intel X-86 architecture, the ALIF3000 promises to deliver pixel-perfect picture quality, audio and USB 2.0 to single or dual screens over a single 1GbE link.
“It was important for us to ensure our customers can move to, and access, virtual environments at their own pace while preserving their initial KVM investment,” explained Adrian Dickens, CEO, Adder Technology.
“The ALIF3000 enables exactly that and has been developed to enable our customers to seamlessly add secure VM access into their existing workflows, at a time that is right for them, without enduring unnecessary costs.”
Thanks to integration with the AdderLink Infinity Manager, IT administrators can clearly define secure user access rights to ensure that target PCs can only be accessed by permitted users.
Adder has also introduced a new range of National Information Assurance Partnership (NIAP) Protection Profile 4.0 secure KVM switches and accessories: the AdderView Secure Range, which promises to “maximise cybersecurity without compromising real-time access to mission-critical computing”.
They support video resolutions up to 4K/60 and include secure desktop switches, a multi-viewer and accessories.
The secure switches combine features such as channel separation, unidirectional data paths and tamper-proof labelling to ensure high levels of security. They are also compatible with Adder’s existing matrix and extension products.
The range includes: KVM switches with an e-paper display and colour-configurable LEDs; a Flexi-Switch supporting up to UHD at 60 frames per second on single- and dual-head computers; a multi-viewer for instant and simultaneous access to multiple data sources; a card reader allowing users to simultaneously authenticate up to four isolated computers; a remote control unit providing secure push button access to any channel on the target PC; and a port expander, to provide an additional port for USB human interface devices including touchscreens.





























No comments yet