In the realm of streaming services, the constant battle to safeguard digital content from piracy and cyber threats persists. While Digital Rights Management (DRM) was once at the forefront of content protection, today’s landscape demands a broader, more holistic security approach. As hackers continually refine their tactics, securing OTT/PayTV streaming applications extends beyond DRM, encompassing app infrastructure, device hardware, and operating systems. This article explores a renewed OTT/PayTV app defense approach, delving into security best practices and strategies that stretch beyond conventional content protection. By adopting a security-first mindset and harmonising backend and app-based defenses, streaming service providers can raise the bar against cyber threats, ensuring the highest standards of content protection and viewer data security.
You are not signed in
Only registered users can read the rest of this article.

Co-producing across borders: “Authenticity has become part of the appeal”
Responsible for more than half of Iceland’s scripted TV output in the past five years, production company Glassriver has adapted to a changing media landscape, becoming experts in navigating international co-productions. CEO Andri Ómarsson explains how these international partnerships are now helping local stories travel further than ever.
.jpg)
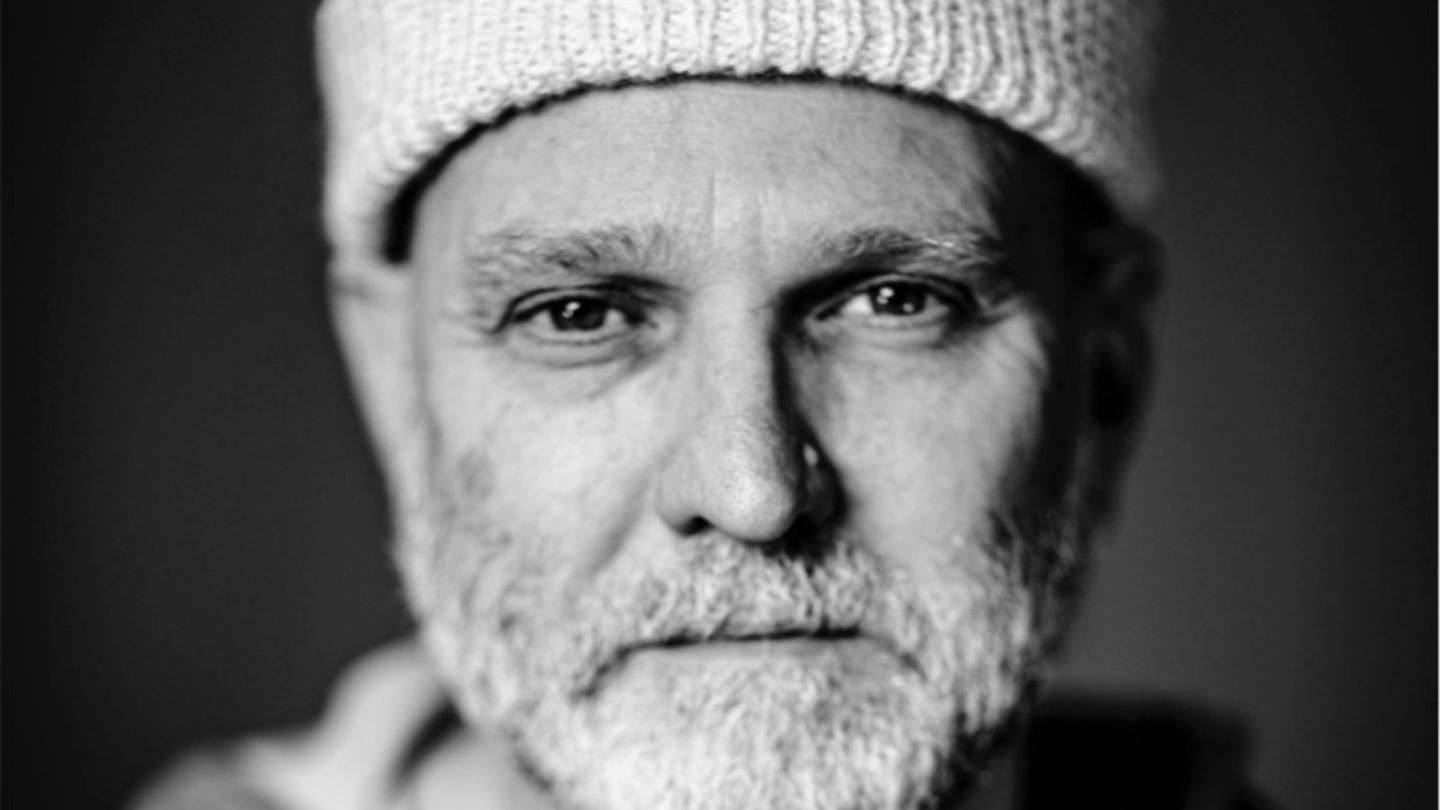
We must go upstream: The financial crisis facing film and TV
Film and TV Charity CEO Marcus Ryder shares his thoughts on the alarming findings from the organisation’s second Money Matters report.
.jpg)
Live video workflows: How IP and 5G are answering the call for low-latency contribution
As production teams seek more streamlined and scalable operations for outside broadcasts, Haivision’s Marcus Schioler considers the evolving role of IP and 5G for the secure, reliable and low-latency transfer of live content.
Virtual production is here: Lean into the learning curve
As VP stands on the cusp of revolutionising the industry, Rob Chandler, Founder of Starting Pixel, explains the importance of understanding the technology to harness its expansive potential.
.jpg)
IP and cloud-driven broadcasts: Why control systems matter more than ever
BFE Studio und Medien Systeme Chief Technology Officer (CTO) Hartmut Opfermann explores how flexible and configurable broadcast control systems will revolutionise media workflows as the industry forays into increasingly complex cloud-native production environments.


